This was a big one.
The dev conference started with a TV series announcement trailer 😑

tvOS 13
- PS4/Xbox One controller support
- New wallpapers
watchOS 6
- New watch faces
- Hourly beeping sound
- Audiobooks, voice memos, calculator
- Independent standalone apps
- Audio streaming API
- Own App Store
- Activity trends
- Noise app to monitor noise pollution
- Cycle tracking
- Health summaries
- New bands
iOS 13
- Speed improvements
- Dark mode
- Improved Safari, Mail, Notes, Reminders
- Improved Maps with Street View (SF only as usual?)
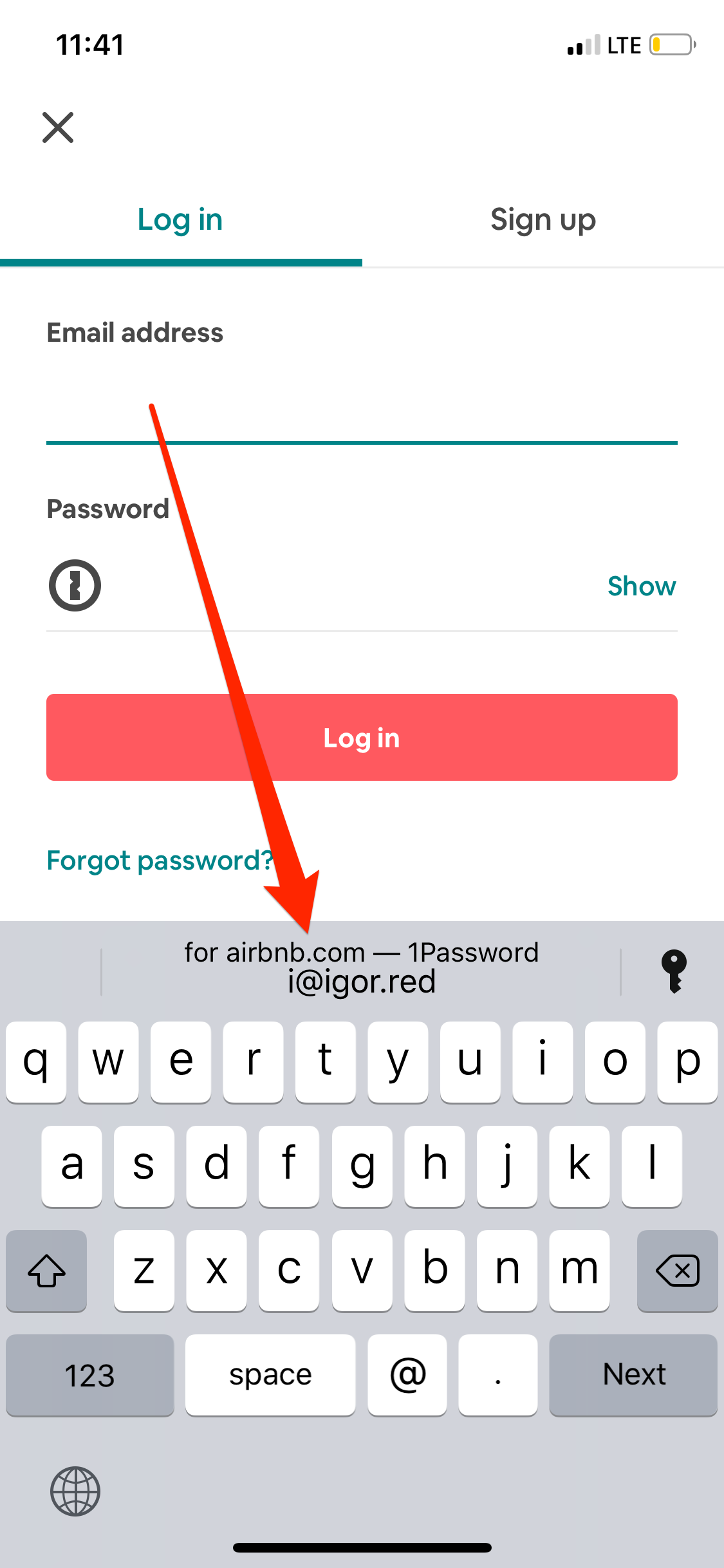
- ‘Just once’ location access option
- Sign in with Apple - private social login
- One-time email address generation
- HomeKit secure video
- iMessage avatar pictures
- Enhanced Memoji with earrings, teeth, eyeshades, etc.
- Memoji stickers
- Improvements to photo capture and post-production
- Rotate videos, filters and effects for videos
- ML to remove photo dupes and choose the best of them
- Improved Photos.app to remove clutter and let focus on important moments
- AirPods reading and replying to messages
- AirPods audio sharing
- HomePod handoff
- Siri live radio support with iHeartRadio, TuneIn, etc. 100k stations.
- Updated CarPlay
- CarPlay integration with 3rd party apps
- Neural TTS - much better sounding Siri voice
iPadOS 1?
- Much improved multitasking
- Multi-window support for the same app
- Improved Files.app
- iCloud Drive folder sharing
- SMB File sharing
- Mass Storage Device support
- External device support via usb-c
- Desktop class browsing on Safari iPad
- Download manager
- Custom fonts
- Working with text is now much easier
- Apple Pencil latency down to 9ms from 20ms
- New notes app
- PencilKit
New Mac Pro
- 28-core Xeon CPU
- 12 DIMM slots
- PCIe expansions
- Special dual-core Vega II GPU
- Custom designed video processing card
- 1.4kW PSU
- Optional wheels
- New 6k, HDR, anti-reflective, 1000 nits display
- Mac pro starts at $5999, new display at $3999/$4999
MacOS 10.15 Catalina
- iTunes now broken down into Apple Music, Podcasts and Apple TV apps
- iPhone sync moves to Finder
- Podcasts will have content search
- Apple TV 4k HDR playback on Mac
- Sidecar - wireless connectivity tablets as second screens/tablets
- Voice control
- Improved find my Mac even when it’s offline
- ScreenTime
Dev Tools
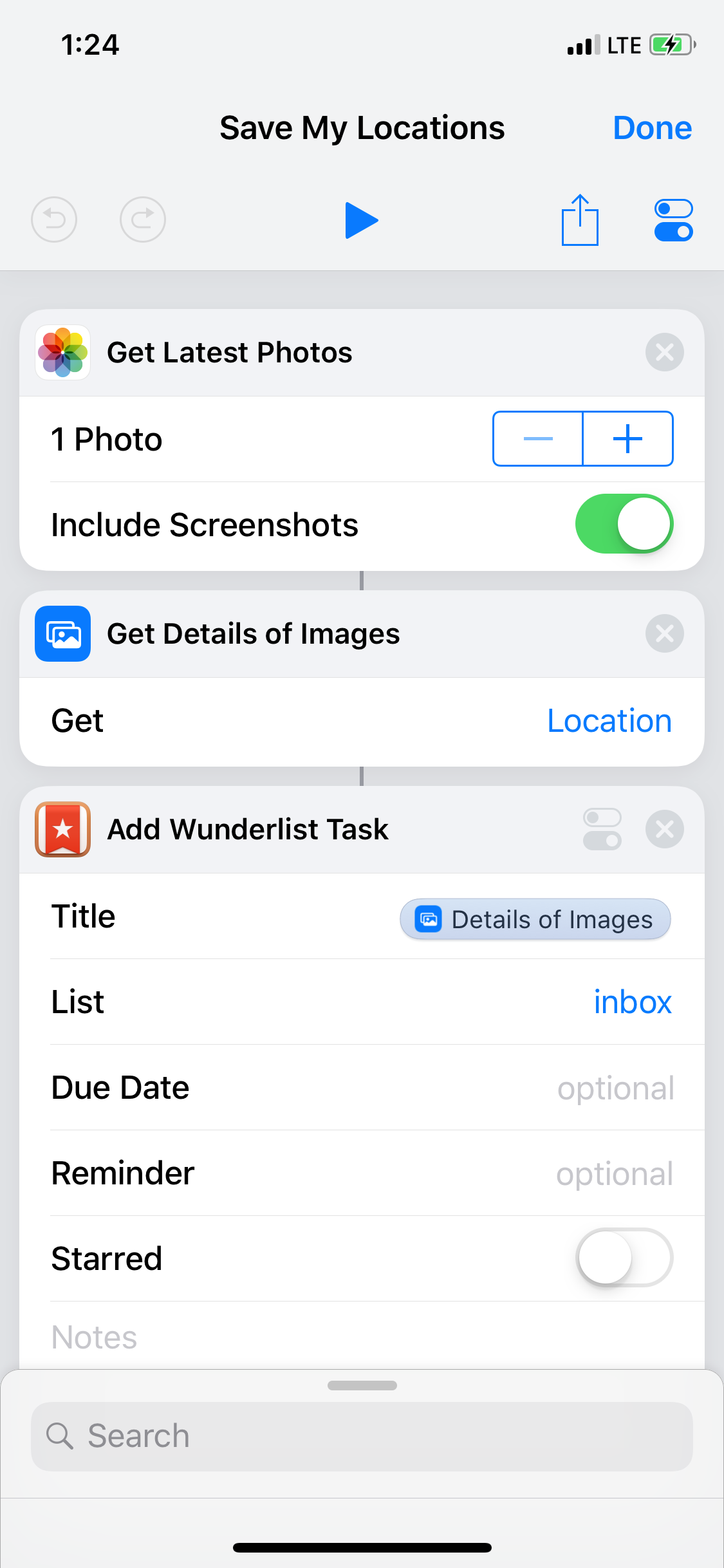
- iPad apps migration tool to Mac
- RealityKit - kit for building photorealistic scenes, includes 3d scene tools
- ARKit3 with real-time people occlusion, motion capture
- Real-world Minecraft
- SwiftUI - new UI framework written in Swift - less code, live preview in sim and device (sic!)
- Native UI framework for watchOS
It was probably the most packed WWDC I've seen. I hope all of the new stuff will be working reliably when it's out 🙂